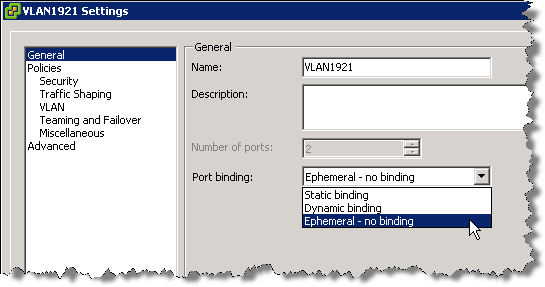
There are 3 types of Port Binding
- Static Binding
- Dynamic Binding
- Ephemeral Binding
Static Binding
When you connect a virtual machine to a port group configured with static binding, a port is immediately assigned and reserved for it, guaranteeing connectivity at all times. The port is disconnected only when the virtual machine is removed from the port group. You can connect a virtual machine to a static-binding port group only through vCenter Server.
Dynamic Binding
In a port group configured with dynamic binding, a port is assigned to a virtual machine only when the virtual machine is powered on and its NIC is in a connected state. The port is disconnected when the virtual machine is powered off or the virtual machine’s NIC is disconnected. Virtual machines connected to a port group configured with dynamic binding must be powered on and off through vCenter.
Dynamic binding can be used in environments where you have more virtual machines than available ports, but do not plan to have a greater number of virtual machines active than you have available ports. For example, if you have 300 virtual machines and 100 ports, but never have more than 90 virtual machines active at one time, dynamic binding would be appropriate for your port group.
Note: Dynamic binding is deprecated in ESXi 5.0.
Ephemeral Binding
In a port group configured with ephemeral binding, a port is created and assigned to a virtual machine by the host when the virtual machine is powered on and its NIC is in a connected state. The port is deleted when the virtual machine is powered off or the virtual machine’s NIC is disconnected.
You can assign a virtual machine to a distributed port group with ephemeral port binding on ESX/ESXi and vCenter, giving you the flexibility to manage virtual machine connections through the host when vCenter is down. Although only ephemeral binding allows you to modify virtual machine network connections when vCenter is down, network traffic is unaffected by vCenter failure regardless of port binding type.
Note: Ephemeral port groups should be used only for recovery purposes when you want to provision ports directly on host bypassing vCenter Server, not for any other case. This is true for several reasons:
The disadvantage is that if you configure ephemeral port binding your network will be less secure. Anybody who will gain host access can create rogue virtual machine and place it on the network or to move VMs between networks. The security hardening guide even recommends to lower the number of ports for each distributed portgroup so there are none unused.
AutoExpand (New Feature)
Note: vSphere 5.0 has introduced a new advanced option for static port binding called Auto Expand. This port group property allows a port group to expand automatically by a small predefined margin whenever the port group is about to run out of ports. In vSphere 5.1, the Auto Expand feature is enabled by default.
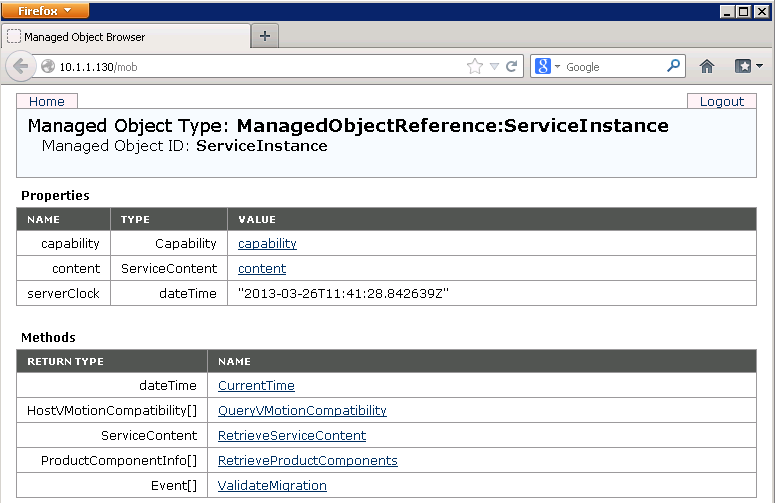
In vSphere 5.0 Auto Expand is disabled by default. To enable it, use the vSphere 5.0 SDK via the managed object browser (MOB):
- In a browser, enter the address http://vc-ip-address/mob/.
- When prompted, enter your vCenter Server username and password.
- Click the Content link.
- In the left pane, search for the row with the word rootFolder.
- Open the link in the right pane of the row. The link should be similar to group-d1 (Datacenters).
- In the left pane, search for the row with the word childEntity. In the right pane, you see a list of datacenter links.
- Click the datacenter link in which the vDS is defined.
- In the left pane, search for the row with the word networkFolder and open the link in the right pane. The link should be similar to group-n123 (network).
- In the left pane, search for the row with the word childEntity. You see a list of vDS and distributed port group links in the right pane.
- Click the distributed port group for which you want to change this property.
- In the left pane, search for the row with the word config and click the link in the right pane.
- In the left pane, search for the row with the word autoExpand. It is usually the first row.
- Note the corresponding value displayed in the right pane. The value should be false by default.
- In the left pane, search for the row with the word configVersion. The value should be 1 if it has not been modified.
- Note the corresponding value displayed in the right pane as it is needed later.
- Note: I found mine said AutoExpand=true and ConfigVersion=3
- Go back to the distributed port group page.
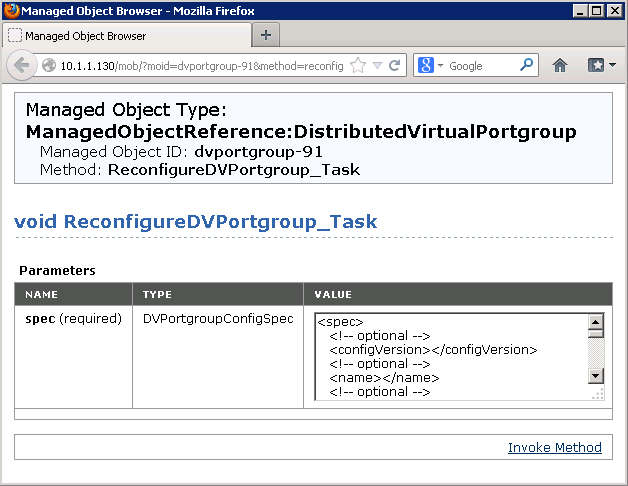
- Click the link at the bottom of the page that reads ReconfigureDv<PortGroup>_Task
- A new window appears.
- In the Value field, find the following lines and adjust them to the values you recorded earlier
<spec>
<configVersion>3</configVersion>
- And scroll to the end and find and adjust this
<autoExpand>true</autoExpand>
</spec>
- where configVersion is what you recorded in step 15.
- Click the Invoke Method link.
- Close the window.
- Repeat Steps 10 through 14 to verify the new value for autoExpand.
Useful VMware Article
Useful Blog on why to use Static Port Binding on vDS Switches
http://blogs.vmware.com/vsphere/2012/05/why-use-static-port-binding-on-vds-.html